Best Remote IoT Device SSH: Your Ultimate Guide To Secure Connections
Hey there, tech enthusiasts! If you're looking for the best remote IoT device SSH options, you're in the right place. Whether you're a seasoned developer or just starting your IoT journey, secure remote access is crucial. In this guide, we’ll dive deep into what makes certain IoT devices stand out when it comes to SSH capabilities. So, buckle up and let’s explore how to keep your devices safe and connected!
When it comes to managing IoT devices remotely, SSH (Secure Shell) is your best friend. It’s not just about convenience; it’s about ensuring that your devices remain secure against potential threats. As IoT continues to grow, the importance of secure communication cannot be overstated.
But why focus on the best remote IoT device SSH solutions? Simple. The right SSH setup can save you time, money, and a lot of headaches. From monitoring home automation systems to managing industrial IoT deployments, SSH offers a reliable way to interact with your devices from anywhere in the world.
Read also:Access Iot Behind Router Unlocking The Hidden Potential Of Your Smart Devices
Why SSH Matters for Remote IoT Devices
SSH isn’t just another protocol; it’s a lifeline for anyone working with IoT devices. Let’s break down why SSH is so important:
- Encryption: SSH ensures that all data transmitted between your device and remote server is encrypted, keeping sensitive information safe.
- Authentication: With SSH, you can verify the identity of both the client and server, reducing the risk of unauthorized access.
- Flexibility: Whether you're running commands, transferring files, or debugging issues, SSH provides the tools you need to manage your IoT devices effectively.
Now, let’s dive into some of the best remote IoT device SSH options available today.
Top Remote IoT Devices with Excellent SSH Capabilities
Choosing the right IoT device with robust SSH support can make all the difference. Here’s a list of some of the best options:
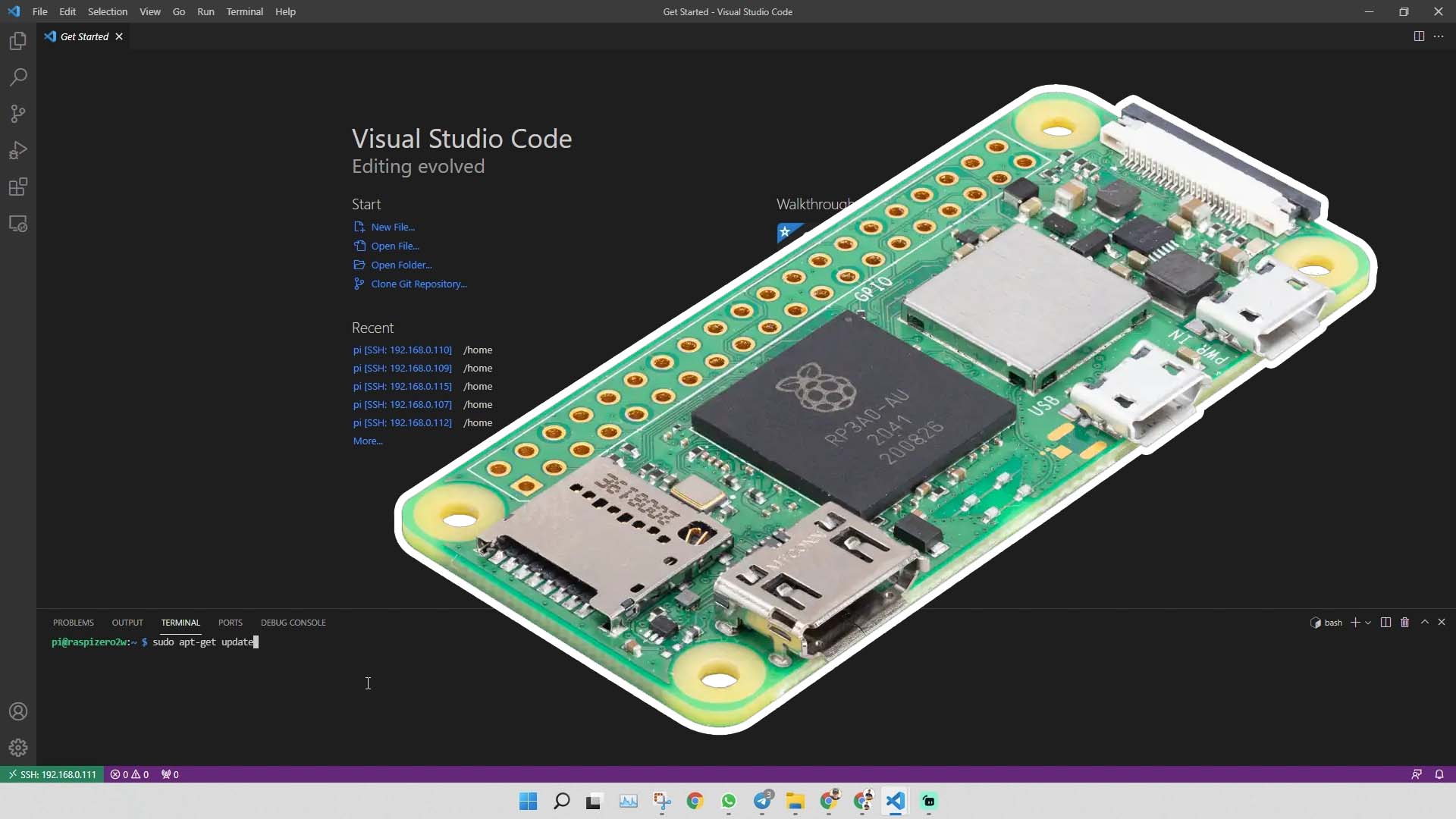
Raspberry Pi: The Ultimate SSH Powerhouse
If you’re familiar with IoT, chances are you’ve heard of the Raspberry Pi. This tiny yet powerful device is a favorite among hobbyists and professionals alike. With built-in SSH capabilities, the Raspberry Pi allows you to securely manage your projects from anywhere.
Key features:
- Cost-effective and easy to set up
- Supports a wide range of operating systems
- Perfect for both small-scale and enterprise-level projects
ESP32: Compact and Feature-Rich
The ESP32 is another gem in the IoT world. Known for its versatility and affordability, this device offers seamless SSH integration. Whether you’re building a smart home system or a weather station, the ESP32 has got you covered.
Read also:Best Remote Iot Device Management Platform Examples You Need To Know
Why choose ESP32?
- Dual-core processor for enhanced performance
- Built-in Wi-Fi and Bluetooth capabilities
- Low power consumption for extended battery life
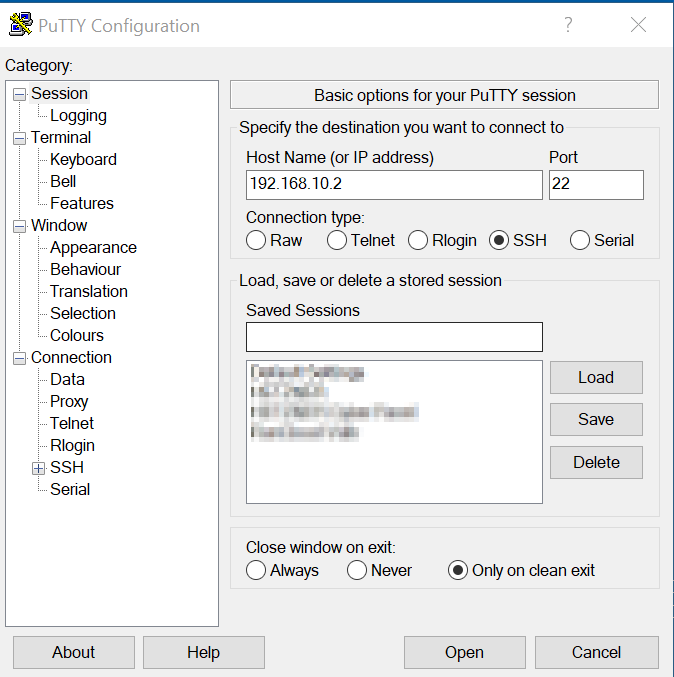
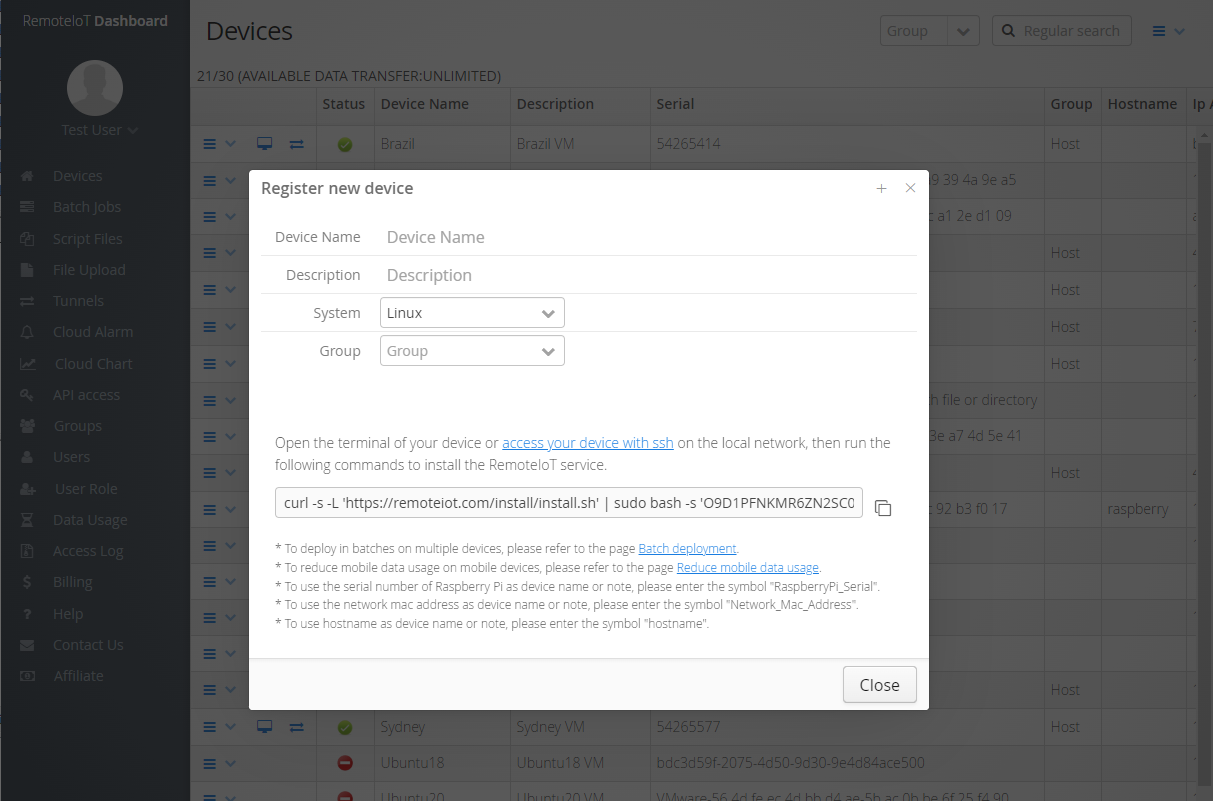
How to Set Up SSH on Your IoT Devices
Setting up SSH on your IoT devices might sound intimidating, but it’s actually pretty straightforward. Follow these steps to get started:
Step 1: Enable SSH on Your Device
Most IoT devices come with SSH disabled by default. To enable it:
- Access your device’s configuration menu
- Look for the SSH settings and toggle it on
- Save your changes and reboot the device
Step 2: Generate SSH Keys
SSH keys provide an added layer of security. Here’s how to generate them:
- Open a terminal or command prompt
- Run the command: ssh-keygen -t rsa
- Follow the prompts to create your public and private keys
Best Practices for Securing Your IoT SSH Connections
While SSH is inherently secure, there are steps you can take to further enhance its protection:
1. Use Strong Passwords
Weak passwords are an open invitation for hackers. Always use strong, unique passwords for your SSH connections.
2. Limit Access
Restrict SSH access to only trusted IP addresses. This reduces the risk of unauthorized access from unknown sources.
3. Regularly Update Your Devices
Keep your IoT devices and firmware up to date. Manufacturers frequently release updates to patch security vulnerabilities.
Data and Statistics: The Growing Importance of IoT Security
According to a recent report by Gartner, the number of IoT devices is expected to reach 25 billion by 2030. With such rapid growth, the need for secure remote access solutions like SSH becomes even more critical.
Here are some eye-opening statistics:
- Over 70% of IoT devices have known security vulnerabilities
- 57% of organizations experienced a security breach due to unsecured IoT devices
- By 2025, the global IoT security market is projected to be worth $36.6 billion
Common Challenges with IoT SSH Connections
While SSH offers numerous benefits, it’s not without its challenges. Here are some common issues you might encounter:
1. Connectivity Issues
Intermittent connectivity can disrupt your SSH sessions. Ensure your devices are connected to a stable network to avoid this problem.
2. Configuration Errors
Misconfiguring SSH settings can lead to failed connections. Double-check your settings and consult the device’s documentation if needed.
Future Trends in IoT SSH Technology
The world of IoT is constantly evolving, and so is SSH technology. Here are some trends to watch out for:
1. Quantum-Resistant Encryption
As quantum computing becomes more prevalent, researchers are developing encryption methods that can withstand quantum attacks. This will further enhance the security of IoT SSH connections.
2. AI-Powered Security
Artificial intelligence is being used to detect and respond to security threats in real-time. Expect to see more AI-driven solutions in the realm of IoT security.
Conclusion: Your Next Steps
And there you have it – a comprehensive guide to the best remote IoT device SSH options. Remember, securing your IoT devices is not just a good practice; it’s a necessity in today’s digital landscape.
So, what’s next? Take action! Here’s what you can do:
- Choose the right IoT device for your needs
- Set up SSH and follow best practices for security
- Stay updated on the latest trends and technologies in IoT security
Feel free to leave a comment below sharing your experiences with IoT SSH or ask any questions you might have. And don’t forget to share this article with your tech-savvy friends!
Table of Contents
- Why SSH Matters for Remote IoT Devices
- Top Remote IoT Devices with Excellent SSH Capabilities
- How to Set Up SSH on Your IoT Devices
- Best Practices for Securing Your IoT SSH Connections
- Data and Statistics: The Growing Importance of IoT Security
- Common Challenges with IoT SSH Connections
- Future Trends in IoT SSH Technology
- Conclusion: Your Next Steps